How to secure your wi-fi network against intrusion

William Smith
Updated on March 29, 2026
February 6, 2020 By Ryan Orsi
Ubiquiti, a global networking technology company came onto the mainstream marketplace beginning in 2005 with a clever idea of offering products at low prices to mass markets guiding channel players to monetize their services instead of the hardware. Every strategy has its pluses and minuses and some would say Ubiquiti’s low-price leader concept swung the pendulum too far, reducing their own ability to re-invest profits into their research and development department. Others would say the low-price leader concept has worked and put the UniFi brand on the map alongside networking names like Cisco Meraki. Regardless of which viewpoint you align to, the number of businesses with Ubiquiti UniFi access points around the world is impressive and therefore a prime target for cyber criminals as evidenced by vulnerability disclosed last year.
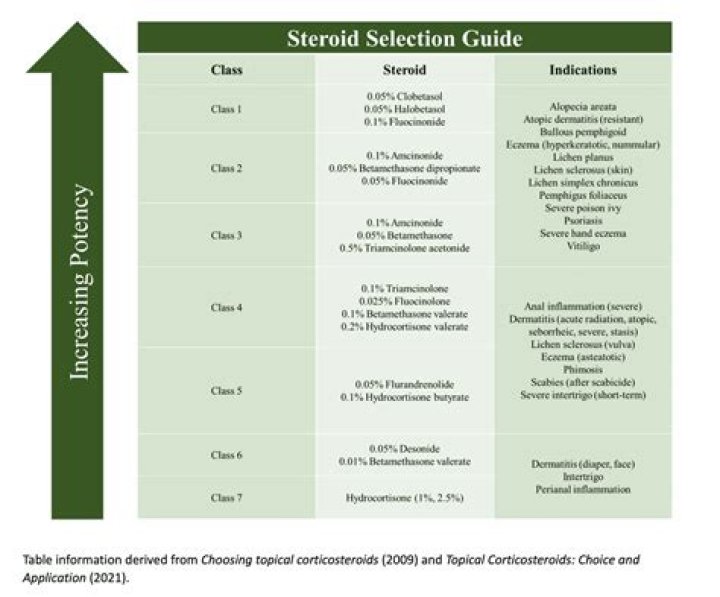
Thinking of how exposed a business would be to eavesdropping, credential theft, and web history/email theft if attackers were to hack past a UniFi access point, Wi-Fi professionals at Miercom, recently tested Ubiquiti’s UniFi Secure HD access point (AP) to determine if it could automatically detect and prevent the six known Wi-Fi threats. The UAP-AC-SHD was only able to automatically detect one of the six threats – the Evil Twin AP – and failed to automatically detect the other five. The UAP-AC-SHD also failed to automatically prevent all six threats. Results are seen in the table below and full test details can be downloaded here. Note the blue columns show the UAP-AC-SHD operating alone and the red columns show it when a WatchGuard AP125 is added to the network to protect the UAP-AC-SHD from Wi-Fi hacks.
If you’re a cyber security expert, you’re likely not surprised at these findings as most Wi-Fi equipment makers have put security on the back burner for years mostly because the general market doesn’t have the exposure to how severe of a problem Wi-Fi hacking is and therefore isn’t top of mind to most buyers. However if you’re not a security expert or if you’re using a Ubiquiti access point right now, you might be a bit shocked. Especially when the UniFi Secure HD AP contains a dedicated radio that “Constantly monitors and protects against threats” as displayed on the website.
Feeling my electrical engineering roots tugging at me, I had to dig deeper to see if there was some kind of technical detail footnote could explain away why the dedicated security radio inside the UAP-AC-SHD appeared to be mostly ineffective at stopping major Wi-Fi hacks. Alas! On page 5 of the UniFi Secure HD AP datasheet was this text with the ol’ asterisk footnote:
Threat Management The UniFi SHD AP’s dedicated security radio provides persistent threat management to act as a Wireless Intrusion Prevention System (WIPS)* and Wireless Intrusion Detection System (WIDS). Such a dedicated radio affords frequency agility – meaning all available Wi-Fi channels are monitored constantly for threats – not just the channels the AP is using.
* Currently full-time rogue access point detection is the main WIPS feature of the dedicated security radio.
My footnote quest was over but I still feel unfulfilled because the UAP-AC-SHD actually failed the Rogue AP detection test causing me to chalk it up to features still under development at Ubiquiti.
You can protect your UniFi APs from Hacking
Miercom test professionals recognized that WatchGuard has been gearing its cloud-managed AP roadmap with unique security feature sets. To determine how existing Ubiquiti UniFi networks can become Trusted Wireless Environment compliant, Miercom configured a WatchGuard AP125 AP as a security sensor dedicated to protecting the UAP-AC-SHD from the six known Wi-Fi threats. The results show that Ubiquiti Wi-Fi networks that would’ve been vulnerable to the six Wi-Fi threats are 100% protected once a WatchGuard AP125 APs was added. From a deployment perspective, network and security administrators will find a simple solution where the UniFi APs continue to connect Wi-Fi users as usual and the WatchGuard APs act as a sort of Wireless Intrusion Prevention System (WIPS) sentry, constantly monitoring the air space and wired network for presence of any of the six threats.
Wi-Fi hacking is a hot topic, but one that’s plagued by ambiguous and often contradictory technical terminology. Thankfully, there is a solution to the problem: the Trusted Wireless Environment. The Trusted Wireless Environment framework succinctly defines the six Layer 2 Wi-Fi hacks that affect nearly every business today and provides a simple test criterion to determine if a Wi-Fi network is protected from each type of attack.
Those interested in testing their own Ubiquiti Wi-Fi networks for Trusted Wireless Environment compliance can follow the Trusted Wireless Environment test guide, and contact Miercom via their website for a more thorough test involving live client workloads. Lastly, if you’re wondering how many WatchGuard APs you need to add to your existing Ubiquiti Wi-Fi network to protect it, any WatchGuard reseller near you has access to a professional service from WatchGuard that will provide you with a predictive simulation survey that determines the recommended number of WatchGuard APs, installation locations, and WIPS/Wi-Fi coverage range.
How Can I Secure My Internet Connection?
If you’re concerned about the security of your home Wi-Fi network—and all the personal data on it—then you need to make sure access to your wireless network is locked down. Network security can feel intimidating if you’re not a technophile, but it’s easier to secure your internet connection than you might think.
What Is Network Security?
Network security keeps unauthorized users and hackers from accessing your Wi-Fi network and the devices that use it. There are a number of common sense practices that will help you secure your network, and a few extras that can ramp up your security level to top-secret.
- Rename routers and networks.
- Use strong passwords.
- Keep everything updated.
- Turn on encryption.
- Use multiple firewalls.
- Turn off the WPS (Wi-Fi protected setup) setting.
- Use a VPN (virtual private network).
How to Secure Wi-Fi: Common Sense Practices for Every Home Network
Below are some of the easiest ways to secure your internet connection. These steps don’t require any special technical knowledge or extra purchases beyond a wireless router.
Rename Routers and Networks
All wireless routers come with a generic username, and many also include a generic password. When you set up the router for the first time, you’ll need to use this generic admin information, but after it’s up and running you should change both. The generic usernames and passwords that come with routers are public record, which makes a hacker’s job easy—especially if you skip changing the router’s factory settings.
After changing the username and password for your wireless router, you should change the name of your home Wi-Fi network. This is called the SSID (service set identifier), and it’s the name that people will see if they are scanning for nearby networks. Default network names often include the brand and model number of the router being used to create the network, which gives hackers valuable information about your Wi-Fi setup.
Avoid tipping off hackers (and keep neighbors from accessing your Wi-Fi) by renaming the network. Be warned that any devices currently connected to your Wi-Fi network will be kicked off after the name change, including smartphones, computers, game systems, smart home devices, etc. You’ll have to update and reconnect all of those devices when you rename the network.
Keep snoops away by hiding the name of your network (or SSID).
“All wireless routers have a setting that allows you to hide the wireless network SSID from being broadcast. If a hacker cannot see it to even know that it exists, they won’t try to hack into it. Your devices can connect to it, and you can add new devices to it because you know the SSID – they do not.”
Use Strong Passwords
You’ve likely heard more about strong passwords than you ever wanted to, but they keep coming up because they’re still one of the best lines of defense against data leaks and hackers. When it comes to setting up a network password that will keep out online miscreants, use the guidelines below.
- Make it long—at least 16 characters is recommended.
- Use a mixture of upper and lowercase letters, numbers, and special characters.
- Don’t use common phrases or personal information.
- Test the strength of your password. You can use a password manager or an online password checker to find out how secure the password is in real time.
- Make sure it’s unique—don’t reuse a password you’ve already used.
- Use a password manager. They help you keep track of your passwords, and some even generate random passwords that are hard for both humans and computers to crack.
In addition to using long, complex passwords on network devices like routers and repeaters, you can exclude other computers from connecting to yours.
“You can enter in the IP address of the computer you access and configure your router from and exclude all others. That way, even if someone were able to “see” your router, they would automatically be rejected from connecting to it by the device since the IP that is trying to log in is not specifically allowed.”
Pete Canavan, IT Security and Personal Safety Expert
Keep Everything Updated
Routers need to be updated on a regular basis. Router manufacturers update the firmware on routers whenever a vulnerability is detected, just like the operating system on your phone or PC. Set a reminder to check your router settings every month to see if there have been any updates.
Turn On Encryption
These days every router on the market includes encryption, and it’s one of the simplest ways to secure your internet connection. Go to your router’s settings and find the security options. Then look for the WPA2 Personal setting. If you don’t see that, select WPA Personal (but this could be a sign that your router is outdated and more vulnerable). Next, set the encryption type to AES. At this point you need to enter a password or network key. This password is different from the one you used for your router and will be used to connect all devices to your Wi-Fi network. Use the strong password guidelines above to create a secure password.
How to Secure Wi-Fi: Taking Network Security to the Next Level
Below are some of the easiest ways to secure your internet connection. These steps don’t require any special technical knowledge or extra purchases beyond a wireless router.
Use Multiple Firewalls
Below are some of the easiest ways to secure your internet connection. These steps don’t require any special technical knowledge or extra purchases beyond a wireless router.
Turn Off the WPS Setting
The WPS, or Wi-Fi protected setup, is the function that lets devices like phones and smart home gadgets pair with your network. This setting is convenient, especially if you have a lot of smart devices to connect, but it leaves an opening for a hacker to get in. Look for the WPS button on your router and turn it off unless you’re actively pairing your devices with the network.
Use a VPN
A VPN (virtual private network) is one of the best ways to secure your internet connection. It acts as a middleman between your connected device and the internet. It hides your activity so that no one (even online advertisers) can see what you’re doing online. You can find free browser-based VPNs or subscribe to a monthly VPN service. This tool is a must-have for when you’re on a public network, but it’s also a smart way to add an extra layer of security to your home Wi-Fi.
Tips about Wi-Fi security because wireless is inherently less secure
Contributing Writer, Network World |
Wi-Fi is one entry-point hackers can use to get into your network without setting foot inside your building because wireless is much more open to eavesdroppers than wired networks, which means you have to be more diligent about security.
But there’s a lot more to Wi-Fi security than just setting a simple password. Investing time in learning about and applying enhanced security measures can go a long way toward better protecting your network. Here are six tips to betters secure your Wi-Fi network.
Use an inconspicuous network name (SSID)
The service set identifier (SSID) is one of the most basic Wi-Fi network settings. Though it doesn’t seem like the network name could compromise security, it certainly can. Using a too common of a SSID, like “wireless” or the vendor’s default name, can make it easier for someone to crack the personal mode of WPA or WPA2 security. This is because the encryption algorithm incorporates the SSID, and password cracking dictionaries used by hackers are preloaded with common and default SSIDs. Using one of those just makes the hacker’s job easier.
(As we discuss later, this vulnerability doesn’t apply to networks using the enterprise mode of WPA or WPA2 security, one of the many benefits of using the enterprise mode.)
Name your network wisely – it something generic but not too common and without revealing the location.
Although it might make sense to name the SSID something easily identifiable, like the company name, address, or suite number, that might not be the best idea either. This is especially true if the network is in a shared building or in close proximity to other buildings or networks. If hackers drive by a congested area and see a dozen different Wi-Fi networks pop-up, they would likely target the one easiest to identify, which could help them understand what they might gain by hacking it. They might also choose one that’s easier to find in a congested area.
To continue reading this article register now
To revist this article, visit My Profile, then View saved stories.
Photograph: Olly Curtis/MacFormat Magazine/Getty Images
To revist this article, visit My Profile, then View saved stories.
Your router is perhaps the most important gadget in your home. It checks all incoming and outgoing traffic, acting as a sentry to make sure that nothing dangerous comes in and nothing sensitive goes out. It controls access to your home Wi-Fi network and through that all of your phones, tablets, laptops, and more. If someone else gains access to that network—whether a remote hacker or your next-door neighbor—it can be quick work to compromise those devices.
With that in mind, it’s essential to keep your router secure. The good news is these steps aren’t too difficult or time-consuming, and they’ll significantly reduce your risk.
These tips will require you to access your router’s settings, which you can typically do through your web browser by typing in an IP address, or if you’re lucky, through an app on your phone. If you’re not sure how to find these settings, check the documentation that came with the router, or run a quick web search using your router’s make and model.
You should be using WPA2 security to guard access to your router, which essentially requires every new device to submit a password to connect. This is enabled by default on just about every router, but if it’s not active on your device, switch it on through your router settings.
It’s a good idea to change the Wi-Fi password on a regular basis. Yes, it means you’ll need to reconnect all your devices again, but it also kicks off any unwelcome visitors who might be lurking. Your router settings panel should give you a list of connected devices, though it might be tricky to interpret.
We’d also recommend changing the password required to access the router settings themselves, as many people just leave the defaults in place—and that means someone who knows the defaults or who can guess them could reconfigure your router. As with any password, make it very hard to guess but impossible to forget.
These password settings should be fairly prominently displayed inside the router settings panel, and if you router is a more recent model, you might well get warnings if the new passwords you pick are too easy to guess or brute force. Before long, WPA2 will give way to WPA3, which offers more set it and forget it security, but until then, pay close attention to your Wi-Fi password hygiene.
Your router runs low-level software called firmware which essentially controls everything the router does. It sets the security standards for your network, defines the rules about which devices can connect, and so on.
Some more modern routers update themselves in the background, but whatever model you have, it’s always worth making sure the firmware is up to date. This means you’ve got the latest bug fixes and security patches, and are protected against whatever exploits have just been discovered.
The process varies from router to router, but as with the password settings, the option to update your router’s firmware shouldn’t be too difficult to find within the router control panel. If you get stuck, check the router documentation or the official support site on the web.
If you’re lucky, the process will be automatic; you might even get alerts on your phone every time a firmware update gets applied, which usually happens overnight. If you’re unlucky, you might have to download new firmware from the manufacturer’s site and point your router towards it. If so, it’s absolutely worth the extra effort.
A lot of routers come with features designed to make remote access from outside your home easier, but unless you need admin-level access to your router from somewhere else, you can usually safely turn these features off from the router settings panel. Besides, most remote access apps work fine without them.
Another feature to look out for is Universal Plug and Play. Designed to make it easier for devices like games consoles and smart TVs to access the web without making you wade through a lot of configuration screens, UPnP can also be used by malware programs to get high-level access to your router’s security settings.
Keeping remote access and UPnP turned on won’t suddenly expose you to the worst of the internet, but if you want to be as safe as possible, turn them off. If it turns out that some of the apps and devices on your network rely on them, you can enable the features again without too much worry.
You should also think about disabling Wi-Fi Protected Setup. WPS has good intentions, letting you connect new devices with a button push or a PIN code, but that also makes it easier for unauthorized devices to gain access; a numerical PIN is easier to brute force than an alphanumerical password. Unless you specifically need it, disable it.
If your router has the option of broadcasting a so-called guest network, take advantage of it. As the name suggests, it means you can grant your guests access to a Wi-Fi connection, without letting them get at the rest of your network—your Sonos speakers, the shared folders on your laptop, your printers, and so on.
It’s not like your friends and family are hackers in disguise, but letting them on your primary network means they might access a file that you’d rather they didn’t, or inadvertently change a setting somewhere that causes you problems. It also puts another speed bump in the way of someone who is secretly trying to get access to your network without your permission—even if they’re able to get on the guest network, they won’t be able to take control of your other devices, or your router.
Your router should have the option to hide the SSID of your main network—basically the name of the network that appears when your devices scan for Wi-Fi. If visitors can’t see this network then they can’t connect to it, but you’ll be able to add devices to it because you’ll know what it’s called. (And if you’re not sure, it’ll be listed in your router settings.)
Despite decades of relative neglect, most routers launched in the last couple of years come with excellent security built in. Manufacturers appreciate the importance of router security and reliability more than ever, so the products are much more user-friendly than they used to be. They now handle lot of the key security settings for you.
With that in mind, one of the highest risks to your router is that it’s compromised by a device that it thinks it can trust—in other words, something on your phone or laptop gets access to it and causes some mischief, perhaps by secretly opening an entry point to your router that can be accessed remotely.
By Nick Mediati
Today’s Best Tech Deals
Picked by PCWorld’s Editors
Top Deals On Great Products
Picked by Techconnect’s Editors
Is your Wi-Fi network at home password-protected? If not, it should be. You might not care if your neighbors use your Wi-Fi connection to surf the Web, but someone with more sinister motives could take advantage of your generosity (and lack of protection) to gain access to data stored on your home PCs.
The easiest way to guard against Wi-Fi interlopers is to encrypt your Wi-Fi network. Afterward you’ll have to enter a password whenever you connect to your Wi-Fi network, but that’s a small price to pay for improved security. Most Wi-Fi routers support WEP, WPA, and WPA2 encryption standards. Be sure to use either the WPA or WPA2 encryption settings, which provide a much higher level of security than WEP encryption.
Another safeguard is to set your router not to broadcast the SSID (your network’s name). With SSID broadcasting disabled, your wireless network won’t be visible to computers nearby, and only people who specifically know your network’s name will be able to find it.
The procedure for locking down your Wi-Fi will vary depending on your router’s model and manufacturer. Check the router’s documentation for instructions.
Note that using a public Wi-Fi network safely entails adopting a different set of security procedures.
By Brian Mastroianni
January 20, 2016 / 6:00 AM / CBS News
How secure is the data you share over your home Wi-Fi connection? Not as secure as you might think, according to experts. Software bugs in ubiquitous devices like Internet routers can leave your personal information at risk to hackers. As we continue to move into an ever-more-connected age, everything from smartphones to Web-connected printers could expose personal data in ways you might not realize.
Six years ago, for the first time ever, the number of Internet-connected devices surpassed the number of people in the world, according to a 2015 report from the Federal Trade Commission. By 2020, there will be an estimated 50 billion connected devices, and by that same year, 90 percent of consumer cars will be connected to the Internet. The FTC warned that while so many companies are creating products for the “Internet of Things” — everything from smart kitchen appliances to children’s toys — they “may not have experience” dealing with security.
The Wall Street Journal recently commissioned a cybersecurity expert to test 20 new home Internet routers and found half had outdated firmware (the program that runs the device) with security flaws, including several with known problems that had not been patched.
In one example cited by the Journal, in 2014 engineers at software company Allegro Software Development Corp. discovered that router manufacturers had been churning out devices for years using old Allegro software instead of a newer version that was updated to fix a security bug. Without the security update, the routers put millions of consumers’ Internet connections at risk of being hacked.
Devices that contain software that is not up to date to plug known security flaws is an all-too-common problem.
“This kind of thing is not new at all,” Peter Tran, GM and senior director at the network security company RSA, told CBS News. But he says it’s becoming an increasingly serious concern as more people work remotely and share data over Wi-Fi.
Trending News
Trending News More
- NASA is celebrating the 25th anniversary of the Hubble Space Telescope with the release of a dramatic new look at a young star cluster 20,000 light years away
- Diamonds In The Montana Rough
- Get ready to play the world’s largest Pac-Man game
- Jupiter may be to thank for life on Earth
- How you’re tracked online — and what you can do about it
Tran said that out of the roughly 4.6 billion workers in the world, 20 percent telecommute at least part-time. That means there are a lot of people going online in their living rooms, not to mention opening their laptops in coffee shops or airports, sharing data over Wi-Fi connections that could be compromised. Even password-protected home connections can be vulnerable if they’re not kept up to date with security patches.
Is this a concern that a lot of people should have? Yes. Is it a concern that a lot of people actually have? No, Tran said.
“It’s easy to get in that mentality. The Verizon cable person sets you up and they will do everything for you and all they care about is getting you on the Web as fast as possible. The average consumer has their network’s broadcast ID and access point easily accessible. All the settings are on the router, they could configure their own firewall, they could do what they need to secure themselves, but that isn’t something they realize,” he said.
Whether the circuit board of your router is outdated is dependent on the manufacturer and the overall consumer supply chain that churns out these devices. The Wall Street Journal notes that manufacturers don’t have much motivation to keep sending updates for older routers.
Now that we live in an era of the “smart home,” with hybrid routers that accommodate television, phone, personal Internet access, and other connected devices, Tran stressed that it’s important that the average consumer remain vigilant.
“Anything that needs a connection to an Internet, anything that is ‘smart,’ is natively unsecure by default. There’s going to be a risk, no matter where you are,” Tran explained. “The way we deliver data now — through the cloud, for instance — needs greater and greater access points wherever you go. Other than your laptop and your device, the huge risk as far as being able to access the core of where your data is residing is the Internet access point. The bigger threat, to me, is how we as individual users are becoming the hub with spokes for would-be cyber criminals to traverse across a multitude of access points.”
So, what can people do to protect themselves and their private data? Tran said that there are some good “Internet hygiene” practices to keep in mind. First, you should ask your service provider whether the firmware, the permanent software programmed into your router’s read-only memory, is up to date. The second is to check out what wireless encryption your provider is using. Thirdly, you should restrict your Internet access point from being discovered outside. For instance, you don’t want “John Doe’s Internet” to be broadcast widely for all to see.
Tran said one basic step that most people neglect to take is to set up a complex password that will be tough for hackers to crack. Instead of something easy like “Jon123,” make sure your password is more involved, and be sure to change it every 90 days, which he stressed decreases the risk that your connection will become compromised.
When going online, make sure your device is communicating directly with your router. Tran says you want to make sure you’re using your own Internet access and not going through “someone else’s connection” by mistake.
He also offered this food for thought: “More and more the problem is the printed circuit board industry itself. Roughly 88 percent of all circuit board manufacturers, those that make routers, for instance, are in Asia. They are in China, Japan, South Korea, and Taiwan. Now, 42 percent of those are all manufactured in mainland China,” Tran said. “There’s a lot of debate right now about the source of state-sponsored cyber attacks, corporate espionage.”
Tran said that while many people worry about where their food is sourced, they take their electronics for granted.
“People look for non-GMO, fair-trade-and-sourced food products,” he said. “They should do the same thing with the tools they use for their Internet connections.”
First published on January 20, 2016 / 6:00 AM
© 2016 CBS Interactive Inc. All Rights Reserved.
How to Secure Your Business WiFi Network
The need and convenience of a business WiFi network make it an essential service for most organizations these days. Unfortunately, many small to medium sized businesses lack the necessary resources and cyber skills needed to secure their network properly. That can be a big problem because an unsecured network leaves the business vulnerable to attacks from hackers who want to steal valuable company data or customer information. Compounding the problem, hackers are increasingly targeting small businesses.
Follow these 10 steps today to secure your network and business information safer.
1. Move Your Router to a Physically Secure Location
Getting around many of the more sophisticated security precautions can be as simple as someone hitting the reset button on your router. It’s vital to double-check that your router is in a secure location with restricted access: a locked cabinet or in an office that is always locked. You can even explore video surveillance options to have the router monitored 24/7.
2. Change the Default Router Login Information
This is another tip that might seem elementary, but the truth is that the majority of hacks happen because targets don’t cover the basics. The first web security precaution to take is setting a quality password and continuing to change it frequently. Most routers come with a default username and password such as “admin”, and lists of default usernames and passwords for various routers can easily be found on the Internet.
The best passwords or passphrases are at least 15 characters long, with a mix of letters, numbers, and special characters. This goes double for the admin username and password that you need to log into the router in order to set the password.
Share this passphrase or keycode with employees only as necessary. Most importantly, change the passphrase on a regular basis (quarterly is recommended) as well as each time an employee leaves the company. You can use something like CloudCracker to test the security of your passwords.
3. Change the Network Name
The service set identifier (SSID) is the name that’s broadcast from your Wi-Fi to the outside world so people can find the network. While you want people to be able to find your network, you don’t want to tell anyone and everyone what make and model of router you’re running. The default name out of the box will frequently be something like “Linksys,” or “Netgear3060,” which tells a potential hacker exactly where to look if they want to find documentation that will help them access your network.
4. Update Your Firmware and Software
It’s not exactly at the top of your to-do list, but it’s still critical to your security: Periodically check to see if there have been any firmware updates for your router. These fixes are introduced to solve specific, documented vulnerabilities, so not patching them up is asking for trouble. This goes double for any network security software that you’re running. Firmware updates usually self-install after downloading, making them a simple step in securing your router.
5. Use WPA2
There are usually a few options on your router for passwords, and you want to make sure that you’re using the default encryption protocol WiFi Protected Access, or WPA. If it’s older, it may be set to an outdated, extremely hackable encryption protocol WEP, or “Wired Equivalent Privacy.” Double check your network settings to clarify if you’re using the best encryption protocol available to you. If your router is older or currently WPA-incompatible, check for a firmware fix (as mentioned above), or consider upgrading to a newer router altogether.
6. Double Up on Firewalls
Most routers have a firewall built in that can protect your internal network against outside attacks, but it might not be automatically activated. It’s generally called something like SPI (stateful packet inspection) or NAT (network address translation). Either way, it should be turned on and enabled in your router settings.
It’s also important to make sure your own software doesn’t send stuff out over the network or the internet without your permission. For that, you’ll want to install firewall software on your PC as well. PC Magazine’s top pick is Check Point ZoneAlarm Pro, but there’s also a default firewall that comes with Windows 8 and 10.
7. Set Up Private Access and Public Access
Having both employees and the public alike on the same network is a recipe for trouble. To separate the traffic, consider using a Service Set Identifier (SSID) to make two separate points of access to your network: a business-grade secure access point for your team, and a public one for customers. This isolates your business’s computers from guests, providing an extra layer of protection.
8. Eliminate Rogue APs
A rogue AP is any unofficial access point to your network. These are often created by someone on your network who has bad connectivity in their office. The problem is that they might not be configured as securely as the rest of your network, giving attackers a window of vulnerability. Take the time to occasionally do access point scanning if your network is large enough.
9. Turn Off WPS
Wi-Fi Protected Setup, or WPS, is the designed to make pairing a device with an encrypted network as easy as pushing a button. The problem is that it makes it simple for anyone with even a moment of physical access to your router to gain a foothold in your network. As we said before, it’s important to keep your router in physically secure location. In addition, consider turning off this function unless you need it for something specific.
10. Limit or Disable DHCP
The Dynamic Host Configuration Protocol (DHCP) server in your router is what IP addresses are assigned to each device on the network. You can limit your DHCP range to theoretically limit the number of things on your network, but that might be impractical with all of the different devices we use today that need a WiFi connection.
You could also simply disable DHCP entirely. This would mean that you’d need to go into each device and manually give them an IP address. This gives you a lot of control, but is fairly labor-intensive, depending on how many devices you need up and running on your network.
What You Can Do Right Now to Secure Your Business WiFi Network
As a small business owner, you might feel like you don’t have any information worth stealing, but that won’t stop hackers from gaining access to your network and taking whatever they can find. Don’t make yourself an easy target. Before you find yourself faced with a network breach, take some simple precautions to ensure that your network is secure.
- Learn more about Cox Business WiFi
- Physically secure your router and devices.
- Change the default configurations and passwords on your router.
- Set up separate public and private networks.
- Take advantage of new firmware and firewall software.
- Contact Cox Business for a professional evaluation of your WiFi security
February 6, 2020 By Ryan Orsi
Ubiquiti, a global networking technology company came onto the mainstream marketplace beginning in 2005 with a clever idea of offering products at low prices to mass markets guiding channel players to monetize their services instead of the hardware. Every strategy has its pluses and minuses and some would say Ubiquiti’s low-price leader concept swung the pendulum too far, reducing their own ability to re-invest profits into their research and development department. Others would say the low-price leader concept has worked and put the UniFi brand on the map alongside networking names like Cisco Meraki. Regardless of which viewpoint you align to, the number of businesses with Ubiquiti UniFi access points around the world is impressive and therefore a prime target for cyber criminals as evidenced by vulnerability disclosed last year.
Thinking of how exposed a business would be to eavesdropping, credential theft, and web history/email theft if attackers were to hack past a UniFi access point, Wi-Fi professionals at Miercom, recently tested Ubiquiti’s UniFi Secure HD access point (AP) to determine if it could automatically detect and prevent the six known Wi-Fi threats. The UAP-AC-SHD was only able to automatically detect one of the six threats – the Evil Twin AP – and failed to automatically detect the other five. The UAP-AC-SHD also failed to automatically prevent all six threats. Results are seen in the table below and full test details can be downloaded here. Note the blue columns show the UAP-AC-SHD operating alone and the red columns show it when a WatchGuard AP125 is added to the network to protect the UAP-AC-SHD from Wi-Fi hacks.
If you’re a cyber security expert, you’re likely not surprised at these findings as most Wi-Fi equipment makers have put security on the back burner for years mostly because the general market doesn’t have the exposure to how severe of a problem Wi-Fi hacking is and therefore isn’t top of mind to most buyers. However if you’re not a security expert or if you’re using a Ubiquiti access point right now, you might be a bit shocked. Especially when the UniFi Secure HD AP contains a dedicated radio that “Constantly monitors and protects against threats” as displayed on the website.
Feeling my electrical engineering roots tugging at me, I had to dig deeper to see if there was some kind of technical detail footnote could explain away why the dedicated security radio inside the UAP-AC-SHD appeared to be mostly ineffective at stopping major Wi-Fi hacks. Alas! On page 5 of the UniFi Secure HD AP datasheet was this text with the ol’ asterisk footnote:
Threat Management The UniFi SHD AP’s dedicated security radio provides persistent threat management to act as a Wireless Intrusion Prevention System (WIPS)* and Wireless Intrusion Detection System (WIDS). Such a dedicated radio affords frequency agility – meaning all available Wi-Fi channels are monitored constantly for threats – not just the channels the AP is using.
* Currently full-time rogue access point detection is the main WIPS feature of the dedicated security radio.
My footnote quest was over but I still feel unfulfilled because the UAP-AC-SHD actually failed the Rogue AP detection test causing me to chalk it up to features still under development at Ubiquiti.
You can protect your UniFi APs from Hacking
Miercom test professionals recognized that WatchGuard has been gearing its cloud-managed AP roadmap with unique security feature sets. To determine how existing Ubiquiti UniFi networks can become Trusted Wireless Environment compliant, Miercom configured a WatchGuard AP125 AP as a security sensor dedicated to protecting the UAP-AC-SHD from the six known Wi-Fi threats. The results show that Ubiquiti Wi-Fi networks that would’ve been vulnerable to the six Wi-Fi threats are 100% protected once a WatchGuard AP125 APs was added. From a deployment perspective, network and security administrators will find a simple solution where the UniFi APs continue to connect Wi-Fi users as usual and the WatchGuard APs act as a sort of Wireless Intrusion Prevention System (WIPS) sentry, constantly monitoring the air space and wired network for presence of any of the six threats.
Wi-Fi hacking is a hot topic, but one that’s plagued by ambiguous and often contradictory technical terminology. Thankfully, there is a solution to the problem: the Trusted Wireless Environment. The Trusted Wireless Environment framework succinctly defines the six Layer 2 Wi-Fi hacks that affect nearly every business today and provides a simple test criterion to determine if a Wi-Fi network is protected from each type of attack.
Those interested in testing their own Ubiquiti Wi-Fi networks for Trusted Wireless Environment compliance can follow the Trusted Wireless Environment test guide, and contact Miercom via their website for a more thorough test involving live client workloads. Lastly, if you’re wondering how many WatchGuard APs you need to add to your existing Ubiquiti Wi-Fi network to protect it, any WatchGuard reseller near you has access to a professional service from WatchGuard that will provide you with a predictive simulation survey that determines the recommended number of WatchGuard APs, installation locations, and WIPS/Wi-Fi coverage range.
What Makes WatchGuard’s Wi-Fi Security Unique?
WIPS or Wireless Intrusion Prevention System is a term from the Wi-Fi industry that refers to the prevention of Wi-Fi threats, and at WatchGuard we have taken it to the next level. Our WIPS is unlike any other competing Wi-Fi security solution on the market. WatchGuard’s patented technology ensures you have the real, accurate, and automated Wi-Fi protection that your business needs.
Each WatchGuard access point (AP) has the flexibility to operate as both an access point and a dedicated WIPS security sensor protecting any 3rd party brand access points.
Take WatchGuard WIPS for a Test Drive
Choose Your Deployment Scenario
Scenario 1: Wi-Fi + WIPS
Deploy WatchGuard APs managed with Wi-Fi Cloud and enjoy Trusted Wireless Environment compliant Wi-Fi, intelligent network visibility and troubleshooting features, captive portals , and location-based analytics.
Scenario 2: WIPS Overlay
Just add WatchGuard APs as a security sensor to your existing infrastructure and protect any 3rd party brand access points 24/7.
In this scenario, you see four Ubiquiti APs providing Wi-Fi access to different client devices and one WatchGuard AP configured as a dedicated WIPS sensor. The WatchGuard AP is not accepting connections from any Wi-Fi client, but is there to simply monitor and protect the Ubiquiti APs 24/7/365.
No matter which scenario you choose for your organization, you need proof that the security solution that defends your business against Wi-Fi attacks can provide automatic protection from the six known Wi-Fi threat categories:
Rogue Access Point
Allows attackers to bypass perimeter security.
Rogue Client
Delivers malware payloads to the network after connecting to malicious APs.
Neighbor Access Point or Client Misassociation
Risks infection from connecting to other SSIDs while in range of the authorized AP.
Ad-Hoc Network
Uses peer-to-peer connections to evade security controls and risk exposure to malware.
“Evil Twin” Access Point
Lures users to connect to it so as to spy on traffic, steal data and infect systems.
Misconfigured Access Point
Opens networks to attack as a result of configuration errors.